Brute Force Login Tool
Techniques for preventing a brute force login attack. What are brute force login attacks and how can I protect my users and applications from them A brute force login attack is one of the most common and least subtle attacks conducted against Web applications. The aim of a brute force attack is to gain access to user accounts by repeatedly trying to guess the password of a user or a group of users. If the Web application does not have any protections in place against this type of attack, its possible for automated tools which are readily available on the Internet to submit thousands of password attempts in a matter of seconds or less, making it easy for an attacker to beat a password based authentication system. A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering a. This interactive brute force search space calculator allows you to experiment with password length and composition to develop an accurate and quantified sense for the. By submitting your personal information, you agree that Tech. Target and its partners may contact you regarding relevant content, products and special offers. You also agree that your personal information may be transferred and processed in the United States, and that you have read and agree to the Terms of Use and the Privacy Policy. Brute force login attacks can be conducted in a number of ways. If the length of the password is known, every single combination of numbers, letters and symbols can be tried until a match is found. However, this is a slow process, especially as the length of the password increases which is why long passwords are better than short. The alternative is to use a list of common words, which is known as a dictionary attack. A dictionary attack will generally try all English words, with the option of adding numbers or doubling up the word as the potential password. This has far fewer combinations, but still has a high chance of finding the correct password. Rather than trying many passwords against one user, another brute force attack method is to try one password against many usernames. This is known as a reverse brute force attack. This technique is worth noting as it is where most account lockout policies fail. Reverse brute force attacks are less common, however, because its often difficult for the attacker to compile a sufficiently large volume of usernames for the reverse attack. Preventing brute force attacks. There are a number of techniques for preventing brute force attacks. The first is to implement an account lockout policy. For example, after three failed login attempts, the account is locked out until an administrator unlocks it. The disadvantage of this method is that multiple accounts can be locked out by one malicious user, causing a denial of service for the victims and lots of work for the administrator. A better, albeit more complicated technique is progressive delays. With progressive delays, user accounts are locked out for a set period of time after a few failed login attempts. The lock out time increases with each subsequent failed attempt. This prevents automated tools from performing a brute force attack and effectively makes it impractical to perform such an attack. Another technique is to use a challenge response test to prevent automated submissions of the login page. Tools such as the free re. CAPTCHA can be used to require the user to enter a word or solve a simple math problem to ensure the user is, in fact, a person. Brute Force Login Tool' title='Brute Force Login Tool' />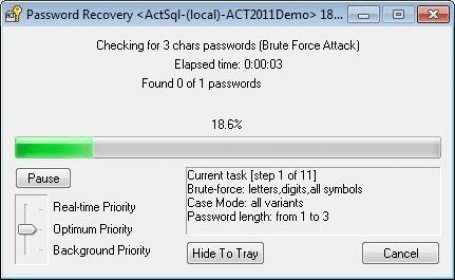 A cipher pronounced SAIfuhr is any method of encrypting text concealing its readability and meaning. It is also sometimes used to refer to the encr. Voc pode criar um ponto de restaurao do Windows, assim, se no gostar do programa ou se ele no funcionar corretamente, voc pode simplesmente restaurar o. This article is about the Linux cipher tool which can be used to encrypt and decrypt some files or folders during a communication process. This technique is effective, but has accessibility concerns and affects usability of the site. Any Web application should enforce the use of strong passwords. At a minimum, requiring users to choose passwords of eight letters or more with some complexity letters and numbers, or requiring one special character is an excellent defence against brute force attacks when combined with one of the techniques outlined above. It may appear, at first, useful to use a tool that automatically reads Web logs and alerts an administrator if multiple attempts come from one IP address. However, it is fairly simple for an attacker to use a variety of tools to automatically and regularly change his or her IP address. MfHba-T4QE/VlrU1_qMWsI/AAAAAAAAANI/yhisui3eFjw/s1600/18599785681_224e635385.jpg' alt='Brute Force Login Tool' title='Brute Force Login Tool' />It is important to ensure the Web application employs at least one of these techniques for defending against brute force attacks if your users are to trust the security of their personal data. Using the techniques outlined in this article should provide a robust defence against this common type of attack. Tear Gas, Guns, Riot Squads The Police States Answer To Free Speech Is Brute Force. Authored by John Whitehead via The Rutherford Institute,Forget everything youve ever been taught about free speech in America. Its all a lie. There can be no free speech for the citizenry when the government speaks in a language of force. What is this language of force Militarized police. Riot squads. Camouflage gear. Black uniforms. Armored vehicles. Mass arrests. Pepper spray. Tear gas. Batons. Strip searches. Surveillance cameras. Kevlar vests. Drones. Lethal weapons. Less than lethal weapons unleashed with deadly force. Rubber bullets. Water cannons. Stun grenades. Arrests of journalists. Crowd control tactics. Intimidation tactics. Brutality. This is not the language of freedom. This is not even the language of law and order. Unfortunately, this is how the government at all levelsfederal, state and localnow responds to those who choose to exercise their First Amendment right to peacefully assemble in public and challenge the status quo. Recently, this militarized exercise in intimidation reared its ugly head in the college town of Charlottesville, Va., where protesters who took to the streets to peacefully express their disapproval of a planned KKK rally were held at bay by implacable lines of gun wielding riot police. Only after a motley crew of Klansmen had been safely escorted to and from the rally by black garbed police did the assembled army of city, county and state police declare the public gathering unlawful and proceed to unleash canisters of tear gas on the few remaining protesters to force them to disperse. To be clear, this is the treatment being meted out to protesters across the political spectrum. The police state does not discriminate. As a USA Today article notes, People demanding justice, demanding accountability or demanding basic human rights without resorting to violence, should not be greeted with machine guns and tanks. Peaceful protest is democracy in action. It is a forum for those who feel disempowered or disenfranchised. Protesters should not have to face intimidation by weapons of war. A militarized police response to protesters poses a danger to all those involved, protesters and police alike. In fact, militarization makes police more likely to turn to violence to solve problems. You want to turn a peaceful protest into a riot Bring in the militarized police with their guns and black uniforms and warzone tactics and comply or die mindset. Ratchet up the tension across the board. Take what should be a healthy exercise in constitutional principles free speech, assembly and protest and turn it into a lesson in authoritarianism. Frankly, any police officer who tells you that he needs tanks, SWAT teams, and pepper spray to do his job shouldnt be a police officer in a constitutional republic. All that stuff in the First Amendment sounds great in theory. However, it amounts to little more than a hill of beans if you have to exercise those freedoms while facing down an army of police equipped with deadly weapons. It doesnt have to be this way. There are other, far better models to follow. For instance, back in 2. St. Louis police opted to employ a passive response to Occupy St. Louis activists. First, police gave the protesters nearly 3. Then, as journalist Brad Hicks reports, when the police finally showed up They didnt show up in riot gear and helmets, they showed up in shirt sleeves with their faces showing. They not only didnt show up with SWAT gear, they showed up with no unusual weapons at all, and what weapons they had all securely holstered. They politely woke everybody up. They politely helped everybody who was willing to remove their property from the park to do so. They then asked, out of the 7. Given 3. 3 hours to think about it, and 1. The rest were advised to please continue to protest, over there on the sidewalk and what happened next was the most absolutely brilliant piece of crowd control policing I have heard of in my entire lifetime. All of the cops who werent busy transporting and processing the voluntary arrestees lined up, blocking the stairs down into the plaza. They stood shoulder to shoulder. They kept calm and silent. They positioned the weapons on their belts out of sight. They crossed their hands low in front of them, in exactly the least provocative posture known to man. And they peacefully, silently, respectfully occupied the plaza, using exactly the same non violent resistance techniques that the protesters themselves had been trained in. As Forbes concluded, This is a more humane, less costly, and ultimately more productive way to handle a protest. This is great proof that police can do it the old fashioned way using their brains and common sense instead of tanks, SWAT teams, and pepper spray and have better results. It can be done. Police will not voluntarily give up their gadgets and war toys and combat tactics, however. Their training and inclination towards authoritarianism has become too ingrained. As I make clear in my book Battlefield America The War on the American People, if we are to have any hope of dismantling the police state, change must start locally, community by community. Citizens will have to demand that police de escalate and de militarize. And if the police dont listen, contact your city councils and put the pressure on them. Remember, they work for us. They might not like hearing itthey certainly wont like being reminded of itbut we pay their salaries. Autodesk Smoke Mac Crack. We must adopt a different mindset and follow a different path if we are to alter the outcome of these interactions with police. The American dream was built on the idea that no one is above the law, that our rights are inalienable and cannot be taken away, and that our government and its appointed agents exist to serve us. It may be that things are too far gone to save, but still we must try.
A cipher pronounced SAIfuhr is any method of encrypting text concealing its readability and meaning. It is also sometimes used to refer to the encr. Voc pode criar um ponto de restaurao do Windows, assim, se no gostar do programa ou se ele no funcionar corretamente, voc pode simplesmente restaurar o. This article is about the Linux cipher tool which can be used to encrypt and decrypt some files or folders during a communication process. This technique is effective, but has accessibility concerns and affects usability of the site. Any Web application should enforce the use of strong passwords. At a minimum, requiring users to choose passwords of eight letters or more with some complexity letters and numbers, or requiring one special character is an excellent defence against brute force attacks when combined with one of the techniques outlined above. It may appear, at first, useful to use a tool that automatically reads Web logs and alerts an administrator if multiple attempts come from one IP address. However, it is fairly simple for an attacker to use a variety of tools to automatically and regularly change his or her IP address. MfHba-T4QE/VlrU1_qMWsI/AAAAAAAAANI/yhisui3eFjw/s1600/18599785681_224e635385.jpg' alt='Brute Force Login Tool' title='Brute Force Login Tool' />It is important to ensure the Web application employs at least one of these techniques for defending against brute force attacks if your users are to trust the security of their personal data. Using the techniques outlined in this article should provide a robust defence against this common type of attack. Tear Gas, Guns, Riot Squads The Police States Answer To Free Speech Is Brute Force. Authored by John Whitehead via The Rutherford Institute,Forget everything youve ever been taught about free speech in America. Its all a lie. There can be no free speech for the citizenry when the government speaks in a language of force. What is this language of force Militarized police. Riot squads. Camouflage gear. Black uniforms. Armored vehicles. Mass arrests. Pepper spray. Tear gas. Batons. Strip searches. Surveillance cameras. Kevlar vests. Drones. Lethal weapons. Less than lethal weapons unleashed with deadly force. Rubber bullets. Water cannons. Stun grenades. Arrests of journalists. Crowd control tactics. Intimidation tactics. Brutality. This is not the language of freedom. This is not even the language of law and order. Unfortunately, this is how the government at all levelsfederal, state and localnow responds to those who choose to exercise their First Amendment right to peacefully assemble in public and challenge the status quo. Recently, this militarized exercise in intimidation reared its ugly head in the college town of Charlottesville, Va., where protesters who took to the streets to peacefully express their disapproval of a planned KKK rally were held at bay by implacable lines of gun wielding riot police. Only after a motley crew of Klansmen had been safely escorted to and from the rally by black garbed police did the assembled army of city, county and state police declare the public gathering unlawful and proceed to unleash canisters of tear gas on the few remaining protesters to force them to disperse. To be clear, this is the treatment being meted out to protesters across the political spectrum. The police state does not discriminate. As a USA Today article notes, People demanding justice, demanding accountability or demanding basic human rights without resorting to violence, should not be greeted with machine guns and tanks. Peaceful protest is democracy in action. It is a forum for those who feel disempowered or disenfranchised. Protesters should not have to face intimidation by weapons of war. A militarized police response to protesters poses a danger to all those involved, protesters and police alike. In fact, militarization makes police more likely to turn to violence to solve problems. You want to turn a peaceful protest into a riot Bring in the militarized police with their guns and black uniforms and warzone tactics and comply or die mindset. Ratchet up the tension across the board. Take what should be a healthy exercise in constitutional principles free speech, assembly and protest and turn it into a lesson in authoritarianism. Frankly, any police officer who tells you that he needs tanks, SWAT teams, and pepper spray to do his job shouldnt be a police officer in a constitutional republic. All that stuff in the First Amendment sounds great in theory. However, it amounts to little more than a hill of beans if you have to exercise those freedoms while facing down an army of police equipped with deadly weapons. It doesnt have to be this way. There are other, far better models to follow. For instance, back in 2. St. Louis police opted to employ a passive response to Occupy St. Louis activists. First, police gave the protesters nearly 3. Then, as journalist Brad Hicks reports, when the police finally showed up They didnt show up in riot gear and helmets, they showed up in shirt sleeves with their faces showing. They not only didnt show up with SWAT gear, they showed up with no unusual weapons at all, and what weapons they had all securely holstered. They politely woke everybody up. They politely helped everybody who was willing to remove their property from the park to do so. They then asked, out of the 7. Given 3. 3 hours to think about it, and 1. The rest were advised to please continue to protest, over there on the sidewalk and what happened next was the most absolutely brilliant piece of crowd control policing I have heard of in my entire lifetime. All of the cops who werent busy transporting and processing the voluntary arrestees lined up, blocking the stairs down into the plaza. They stood shoulder to shoulder. They kept calm and silent. They positioned the weapons on their belts out of sight. They crossed their hands low in front of them, in exactly the least provocative posture known to man. And they peacefully, silently, respectfully occupied the plaza, using exactly the same non violent resistance techniques that the protesters themselves had been trained in. As Forbes concluded, This is a more humane, less costly, and ultimately more productive way to handle a protest. This is great proof that police can do it the old fashioned way using their brains and common sense instead of tanks, SWAT teams, and pepper spray and have better results. It can be done. Police will not voluntarily give up their gadgets and war toys and combat tactics, however. Their training and inclination towards authoritarianism has become too ingrained. As I make clear in my book Battlefield America The War on the American People, if we are to have any hope of dismantling the police state, change must start locally, community by community. Citizens will have to demand that police de escalate and de militarize. And if the police dont listen, contact your city councils and put the pressure on them. Remember, they work for us. They might not like hearing itthey certainly wont like being reminded of itbut we pay their salaries. Autodesk Smoke Mac Crack. We must adopt a different mindset and follow a different path if we are to alter the outcome of these interactions with police. The American dream was built on the idea that no one is above the law, that our rights are inalienable and cannot be taken away, and that our government and its appointed agents exist to serve us. It may be that things are too far gone to save, but still we must try.
